CIPA audit checklist preview
Below is a preview of the kinds of technical and documentary controls included in the CIPA audit checklist. The downloadable version can be used as a working review document in Excel or PDF format.
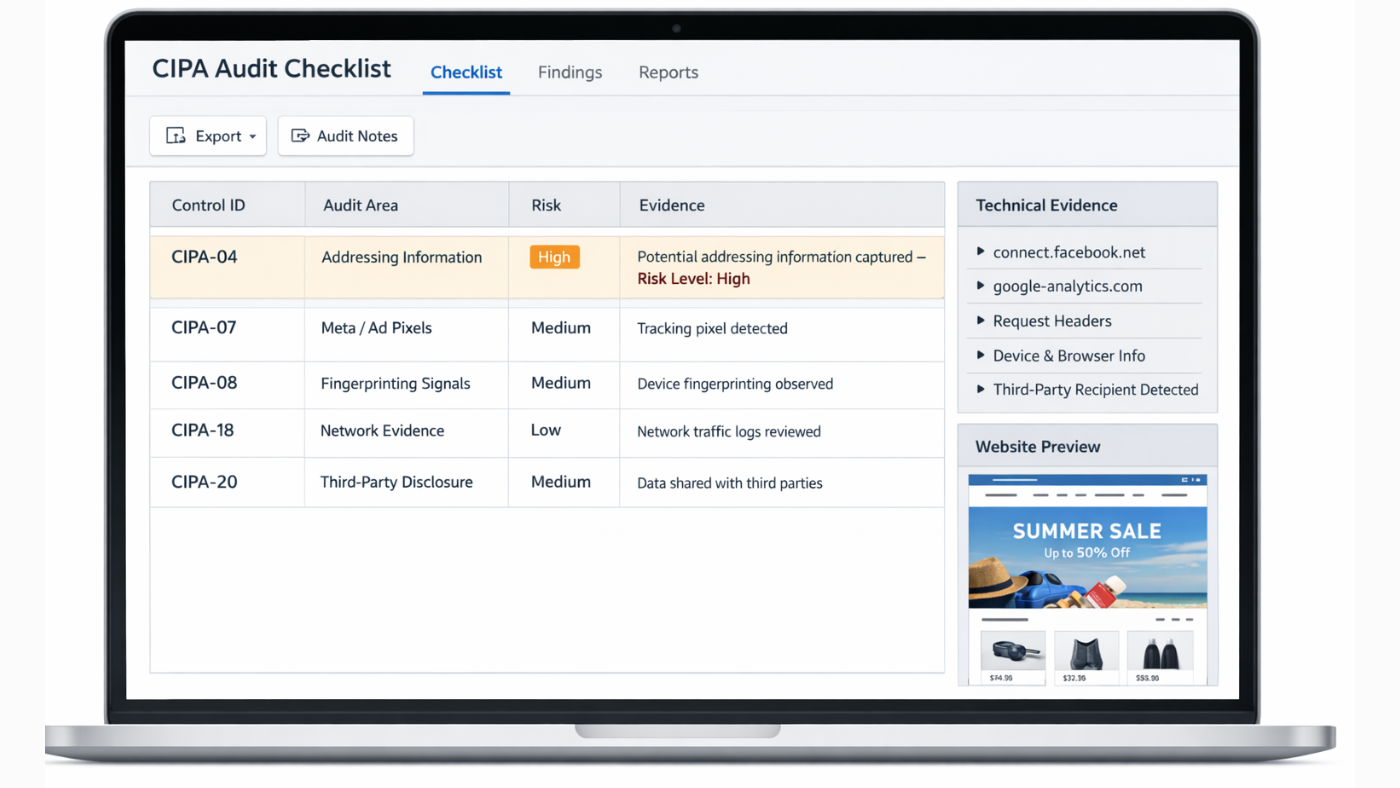
Preview of the CIPA audit checklist used to review website tracking technologies, addressing information signals, and evidence capture.
| Checklist Area | Sample Review Questions |
|---|---|
| Addressing Information | Do scripts or requests capture IP-related or signaling data during page visits? |
| Third-Party Pixels | Do Meta Pixel or other ad-tech tools transmit identifiers or request metadata to external recipients? |
| Fingerprinting Signals | Are browser, device, or environmental signals collected in ways that may support user correlation? |
| Consent and Disclosure | Do disclosures clearly explain the actual tracking behavior observed during testing? |
| Evidence Capture | Are HAR files, DevTools screenshots, and request traces preserved for review? |
| Third-Party Recipients | Can external recipients of addressing or signaling information be clearly identified? |